FTPS
HTTP
** HTTPS
WEP2
TFTP
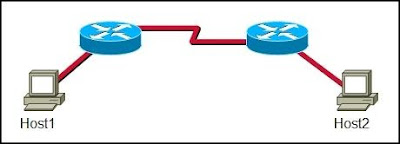
2 Refer to the exhibit. A new branch office has been added to the corporate network and a new router is to be installed to allow branch office users to access the database server at headquarters. How should the serial 0/0/0 interface of the new branch office router be configured to connect to the headquarters router?
branch_23(config-if)# ip address 192.168.5.19 255.255.255.240
branch_23(config-if)# no shutdown
branch_23(config-if)# encapsulation hdlc
branch_23(config-if)# ip address 192.168.5.25 255.255.255.240
branch_23(config-if)# no shutdown
branch_23(config-if)# encapsulation ppp
branch_23(config-if)# no shutdown
branch_23(config-if)# encapsulation ppp
branch_23(config-if)# ip address 192.168.5.33 255.255.255.240
**branch_23(config-if)# encapsulation ppp
branch_23(config-if)# ip address 192.168.5.21 255.255.255.240
branch_23(config-if)# no shutdown
3Which two commands ensure that any password that permits access to the privileged EXEC mode is not shown in plain text when the configuration files are displayed? (Choose two.)
** Router(config)# enable secret cisco
Router(config)# enable cisco
Router(config)# encryption-password all
Router(config)# enable login encrypted
Router(config)# enable password encryption
** Router(config)# service password-encryption
4A new network is to be configured on a router. Which of the following tasks must be completed to configure this interface and implement dynamic IP routing for the new network? (Choose three.)
** Select the routing protocol to be configured.
** Assign an IP address and subnet mask to the interface
Update the ip host configuration information with the device name and new interface IP address.
** Configure the routing protocol with the new network IP address.
Configure the routing protocol with the new interface IP address and subnet mask.
Configure the routing protocol in use on all other enterprise routers with the new network information.
5 How does TCP ensure the reliable transfer of data?
if data segments are not received from the source, the destination requests that the segments be resent.
If an acknowledgment of the transmitted segments is not received from the destination in a predetermined amount of the time, the source resends the data.
** TCP uses the SYN-ACK portion of the three-way handshake to ensure that all data has been received.
The TCP Protocol Interpreter process verifies the transmitted data at source and destination.
6 A network administrator is asked to design a system to allow simultaneous access to the Internet for 250 users. The ISP for this network can only supply five public IPs. What can be used to accomplish this task?
routable translation
dynamic translation
static translation
** port address translation
7What is the most commonly used exterior routing protocol?
** BGP
RIP
OSPF
EIGRP
8 Refer to the exhibit. The network administrator needs to configure the router with a name. Which command will the administrator use to configure the router name?
Router# ip hostname Boise
Router# enable hostname Boise
Router(config-line)# name Boise
** Router(config)# hostname Boise
Router(config)# ip hostname Boise
9Why are port numbers included in the TCP header of a segment?
to indicate the correct router interface that should be used to forward a segment
to identify which switch ports should receive or forward the segment
** to determine which Layer 3 protocol should be used to encapsulate the data
to enable a receiving host to forward the data to the appropriate application
to allow the receiving host to assemble the packet in the proper order
10What is the purpose of the routing process?
to encapsulate data that is used to communicate across a network
** to select the paths that are used to direct traffic to destination networks
to convert a URL name into an IP address
to provide secure Internet file transfer
to forward traffic on the basis of MAC addresses
11Which two statements are true about the use of the debug ip rip command on a Cisco router? (Choose two.)
** The debug ip rip command displays RIP routing activity in real time.
**The debug ip rip command can be issued at the user EXEC configuration mode.
The debug ip rip command displays a combination of the information that is displayed by the show ip route and show ip protocols commands.
Because of router processor usage, the debug ip rip command should be used only when necessary.
The debug ip rip command should be used instead of the show ip route command whenever possible.
12What minimum configurations must be set on a host to allow a request to be sent to http://www.cisco.com/? (Choose four.)
**DNS server
WINS server
**IP address
NetBIOS
** subnet mask
** default gateway
13A Catalyst 2960 switch has been taken out of storage to be used as a temporary replacement for another switch that needs to be repaired. About a minute after the switch has started, the SYST LED on the front of the switch transitions from blinking green to amber. What is the meaning of the amber SYST LED?
The switch has no configuration file in NVRAM.
** The switch has failed POST and must be sent for service.
The switch is functioning properly.
The switch is in half-duplex mode.
14Refer to the exhibit. Which combination of cables and symbols is correct?
A - crossover, B - straight-through, C - straight-through
A - crossover, B - rollover, C - straight-through
**A - straight-through, B -crossover, C - straight-through
A - straight-through, B -straight-through, C - straight-through
A - straight-through, B - straight-through, C - crossover
A - rollover, B - straight-through, C - straight-through
15After an unsuccessful ping to the local router, the technician decides to investigate the router. The technician observes that the lights and fan on the router are not operational. In which layer of the OSI model is the problem most likely occurring?
transport
network
data link
** physical
16What are three characteristics of the TCP protocol? (Choose three.)
exchanges datagrams unreliably
is used to send IP error messages
forces the retransmission of unacknowledged packets
** creates a virtual session between end-user applications
**carries the IP address of the destination host in the TCP header
is responsible for breaking messages into segments and reassembling them at their destination
17Refer to the exhibit. The network shown is connected using services from the same ISP. How will the Fohi router dynamically learn routes to the 192.168.16.16/28, 192.168.16.32/28, and 192.168.16.64/28 subnetworks?
with BGP
**with a static route
with a directly connected route
with an interior routing protocol
18Refer to the exhibit. Which type of UTP cable should be used to connect Host A to Switch1?
rollover
console
crossover
**straight-through
19When customers use credit cards to make purchases at a small business, a modem is heard dialing a telephone number to transfer the transaction data to the central office. What type of WAN serial connection is in use?
leased line
packet switched
** circuit switched
point-to-point
20 A user reports being unable to access the Internet. The help desk technician employs a bottom-up approach to troubleshooting. The technician first has the user check the patch cable connection from the PC to the wall, and then has the user verify that the NIC has a green link light. What will the technician have the user do next?
Enter an IP address into the WWW browser address bar to see if DNS is at fault.
Use traceroute to identify the device along the path to the ISP that may be at fault.
** Verify the IP address, subnet, and gateway settings using ipconfig on the PC .
Connect to the user home router to check firewall settings for blocked TCP ports.
21 A ping 192.1.1.20 command is issued on workstation A to determine if workstation B can be reached. What events will occur if this command is successful? (Choose two.)
The router will block the ping request message.
The router will reply to the echo request with a proxy ping response.
Workstation A will send a UDP ping request message to workstation B.
Workstation B will send a UDP ping reply message to workstation A.
** Workstation A will send an ICMP echo request message to workstation B.
** Workstation B will send an ICMP echo reply message to workstation A.
22How does a router know of paths to destination networks? (Choose two.)
**inspection of the destination IP address in data packets
ARP requests from connected routers
manual configuration of routes
** updates from other routers
DHCP information broadcasts
updates from the SMTP management information base
23Refer to the exhibit. Which two statements describe the data conversation shown? (Choose two.)
** The data conversation was started by the HTTP application process running on the client.
The data conversation is identified by TCP port 80 on the client.
The user started the data conversation by sending an e-mail.
The IP address of the Internet server is 192.168.17.43 .
**The Internet server will send data to port 8547 on the client.
24What is one purpose of the TCP three-way handshake?
sending echo requests from the source to the destination host to establish the presence of the destination
determining the IP address of the destination host in preparation for data transfer
requesting the destination to transfer a binary file to the source
**synchronizing sequence numbers between source and destination in preparation for data transfer
25Which type of address is 192.168.17.111/28?
host address
network address
**broadcast address
multicast address
26A customer reports connectivity problems to an ISP technician. Upon questioning the customer, the technician discovers that all network applications are functioning except for FTP. What should the technician suspect is the problem?
** misconfigured firewall
bad port on switch or hub
misconfigured IP addressing on the customer's workstation
wrong DNS server configured on the customer's workstation
wrong default gateway configured on the customer's workstation
27The show ip route command was executed on one of the routers shown in the graphic and the following output was displayed:
C 192.168.4.0/24 is directly connected, Serial0/0
R 192.168.5.0/24 [120/1] via 192.168.4.2, 00:00:19, Serial0/0
R 192.168.1.0/24 [120/2] via 192.168.3.1, 00:00:20, Serial0/1
R 192.168.2.0/24 [120/2] via 192.168.3.1, 00:00:20, Serial0/1
C 192.168.3.0/24 is directly connected, Serial0/1
From which router was this command executed?
A
B
C
D
28Refer to the exhibit. Which two sets of commands are required to configure passwords for all management ports on a Catalyst 2960 switch? (Choose two.)
ALSwitch(config)# interface vlan 1
ALSwitch(config-if)# password cisco
ALSwitch(config-if)# login
**ALSwitch(config)# line vty 0 4
ALSwitch(config-line)# password cisco
ALSwitch(config-line)# login
ALSwitch(config)# line vty 0 15
ALSwitch(config-line)# password cisco
ALSwitch(config-line)# login
ALSwitch(config)# enable secret class
ALSwitch(config)# enable password cisco
ALSwitch(config)# interface fa0/1
ALSwitch(config-if)# password cisco
ALSwitch(config-if)# no shutdown
**ALSwitch(config)# line cons 0
ALSwitch(config-line)# password cisco
ALSwitch(config-line)# login
29A user reports being able to access the Internet but not being able to download e-mail from the mail server at the ISP. What should the user check on the user workstation?
** the POP3 and SMTP server settings in the e-mail application
the patch cable connections at the back of the workstation and at the wall plate
the DHCP settings in the operating system
the IP address, mask, and default gateway values
the NIC drivers
30Refer to the graphic. Which command will configure a static route on Router A to direct traffic from LAN A that is destined for LAN C?
RouterA(config)# ip route 192.168.4.0 255.255.255.0 192.168.5.2
RouterA(config)# ip route 192.168.4.0 255.255.255.0 192.168.3.2
**RouterA(config)# ip route 192.168.5.0 255.255.255.0 192.168.3.2
RouterA(config)# ip route 192.168.3.0 255.255.255.0 192.168.3.1
RouterA(config)# ip route 192.168.3.2 255.255.255.0 192.168.4.0
31Which subnet masks could be used when subnetting a Class B IP address? (Choose two.)
255.255.255.240
** 255.255.192.0
** 255.255.0.0
255.192.0.0
240.0.0.0
255.0.0.0
32 Refer to the exhibit. The network administrator has configured the RTA and RTB interfaces. In order to allow hosts that are attached to RTA to reach the server that is attached to RTB, a static route from RTA to the server LAN and a default route from RTB back to RTA need to be configured. Which two commands will the administrator use to accomplish these tasks on the two routers? (Choose two.)
**RTA(config)# ip route 10.16.10.5 255.255.255.252 10.16.10.6
RTA(config)# ip route 0.0.0.0 0.0.0.0 10.16.10.6
RTA(config)# ip route 10.16.10.96 255.255.255.252 10.16.10.6
RTB(config)# ip route 10.16.10.6 255.255.255.248 10.16.10.6
**RTB(config)# ip route 0.0.0.0 0.0.0.0 S0/0/1
RTB(config)# ip route 0.0.0.0 0.0.0.0 10.16.10.6
33How do port filtering and access lists help provide network security?
**They prevent specified types of traffic from reaching specified network destinations.
They alert network administrators to various type of denial of service attacks as they occur.
They prevent viruses, worms, and Trojans from infecting host computers and servers.
They enable encryption and authentication of confidential data communications.
34 Refer to the exhibit. The network administrator of the building in the graphic needs to choose the type of cable best suited to add ServerB to the network. Which cable type is the best choice?
STP
UTP
coaxial
**fiber optic
35What is used by a routing protocol to determine the best path to include in the routing table?
Convergence time
Default distance
** Metric
Type of router
36Refer to the exhibit. Which IP addresses could be assigned to the hosts in the diagram? (Choose two.)
192.168.65.31
192.168.65.32
** 192.168.65.35
** 192.168.65.60
192.168.65.63
192.168.65.64
37Given the network 192.168.25.0 shown in the graphic, which subnet mask would accommodate the number of hosts in each subnet?
255.255.0.0
255.255.224.0
255.255.255.0
** 255.255.255.224
255.255.255.240
255.255.255.248
38 Which two protocols allow network devices to report their status and events to a centralized network management device? (Choose two.)
** Syslog
Telnet
HTTP
HTTPS
** SNMP
39What is true regarding the differences between NAT and PAT?
PAT uses the word "overload" at the end of the access-list statement to share a single registered address.
Static NAT allows an unregistered address to map to multiple registered addresses.
Dynamic NAT allows hosts to receive the same global address each time external access is required.
**PAT uses unique source port numbers to distinguish between translations.
40Refer to the exhibit. The graphic shows the output of a command issued on router RTB. According to the output, what two statements are true of router RTB? (Choose two.)
**The router is connected to a router named Boise.
Router RTB is connected to a Cisco 1841 router.
Router RTB is directly connected to two other routers.
**The IP address of the router interface connected to router RTB is 192.168.2.6 .
The RTB router is connected to two Cisco devices by Fast Ethernet links.
41Refer to the exhibit. The network administrator uses the command below to configure a default route to the ISP network :
RTB(config)# ip route 0.0.0.0 0.0.0.0 10.1.1.6
A ping issued from the ISP is successful to router RTB. However, ping echo request packets arrive at a host that is attached to the Fa0/0 interface of RTB, and the replies do not make it back to the ISP router. What will fix this problem?
The ISP must be configured to forward packets from the 192.168.1.0 network.
**The ip route command needs to be edited so that the next hop address is 10.1.1.5.
The ip route command needs to be edited so that the 192.168.1.1 address is the next hop address.
The ip route command should be removed from the RTB router configuration.
42 A network technician is using a network management station to gather data about the performance of devices and links within the ISP. Which application layer protocol makes this possible?
**SNMP
FTP
DHCP
SMTP
43What are two purposes of DNS? (Choose two.)
to dynamically assign IP addressing information to network hosts
to simplify the administration of host and default gateway addressing on client computers
to assign TCP port numbers to hosts as part of the data transfer process
**to resolve human-readable domain names to numeric IP addresses
**to replace the static HOSTS file with a more practical dynamic system
44A hacker attempts to reach confidential information that is stored on a server inside the corporate network. A network security solution inspects the entire packet, determines that it is a threat, and blocks the packet from entering the inside network. Which security measure protected the network?
an IDS
**an IPS
a host-based firewall
Anti-X software
45 How many host addresses may be assigned on each subnetwork when using the 130.68.0.0 network address with a subnet mask of 255.255.248.0?
30
256
**2046
2048
4094
4096
46In an IPv4 environment, what information is used by the router to forward data packets from one interface of a router to another?
**destination network address
source network address
source MAC address
well known port destination address
47 A small tire retailer requires a low-cost WAN connection to its headquarters in order to manage its inventory and process customer sales in real time. Which WAN connection type is best suited to its needs?
Sonet
T3
**dialup
DSL
leased line
48The command copy tftp running-config has been entered on the router. What will this command do?
copy the configuration in RAM to a server
**copy the configuration file from a server to RAM
copy the configuration file in NVRAM to RAM
copy the configuration file in NVRAM to a server
copy the configuration file from a server to NVRAM
49Refer to the exhibit. The network administrator needs to configure the Fa0/0 interface of RTB so that hosts from RTA can connect to the server that is attached to RTB. Which two commands will the administrator use to accomplish this task? (Choose two.)
RTB# ip address 192.168.102.98 255.255.255.248
RTB(config-if)# ip address 192.168.102.99 255.255.255.252
RTB(config)# ip address 192.168.102.97 255.255.255.252
RTB(config)# no shutdown
**RTB(config-if)# no shutdown
**RTB(config-if)# ip address 192.168.102.97 255.255.255.252
50Refer to the exhibit. A NOC technician at an ISP enters the command shown. What are two reasons to use this command? (Choose two.)
to map the path to 192.168.1.7
**to test reachability to 192.168.1.7
to locate connectivity problems along the route to 192.168.1.7
to identify the ISPs that interconnect the NOC with the remote host with the address 192.168.1.7
**to measure the time that packets take to reach 192.168.1.7 and return to the technician's workstation